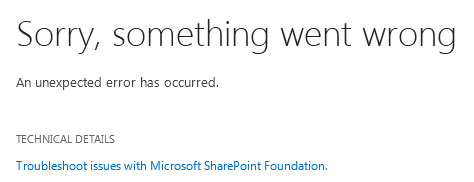
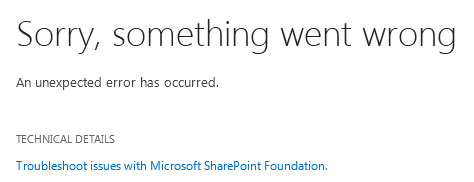
While trying to set up Reporting Services for SharePoint 2013, I ran into a “Something went wrong” message in Reporting Services.
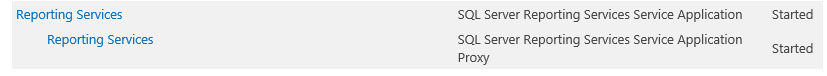
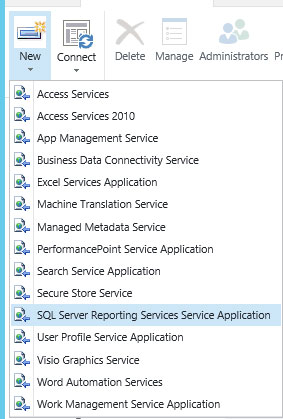
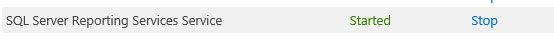
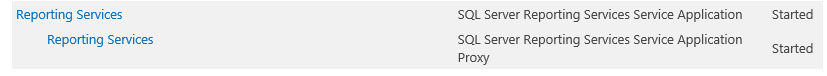
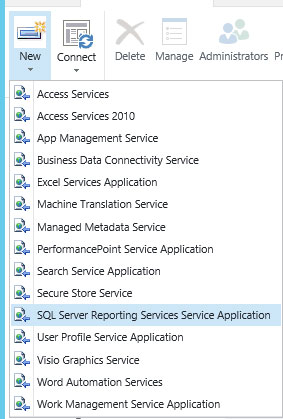
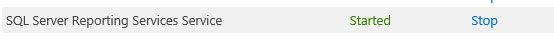
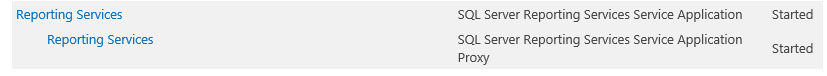
The confusing part is that I was able to provision SQL Server Reporting Services, both verifying that the service was indeed “STARTED” and that I had successfully created a service application and proxy using the GUI from Central Admin.

Clicking on the application (“Reporting Services”) brought me to the configuration area, however, when I went in to set it up, I received an error message stating: “Sorry, something went wrong”.
This left me scratching my head. I determined that the SQL 2012 feature: “Reporting Services – SharePoint” must not have been successfully installed.
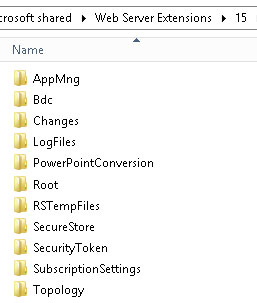
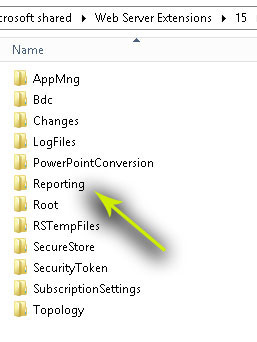
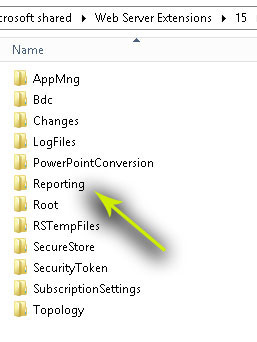
To check this, you will want to go to C:\Program Files\Common Files\microsoft shared\Web Server Extensions\15\WebServices. Once here, look for the “Reporting” folder.
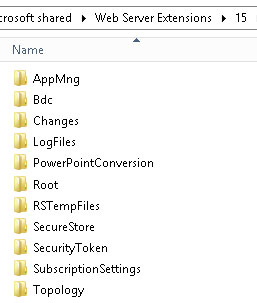
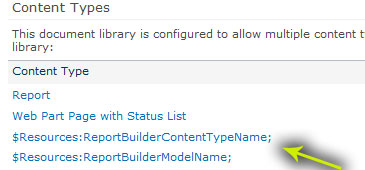
As you can see, there is no “Reporting” folder. It is missing entirely. To remedy this, I first attempted to install the feature via my SSRS 2012 SP1 installation disc.
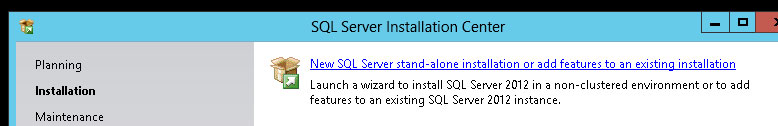
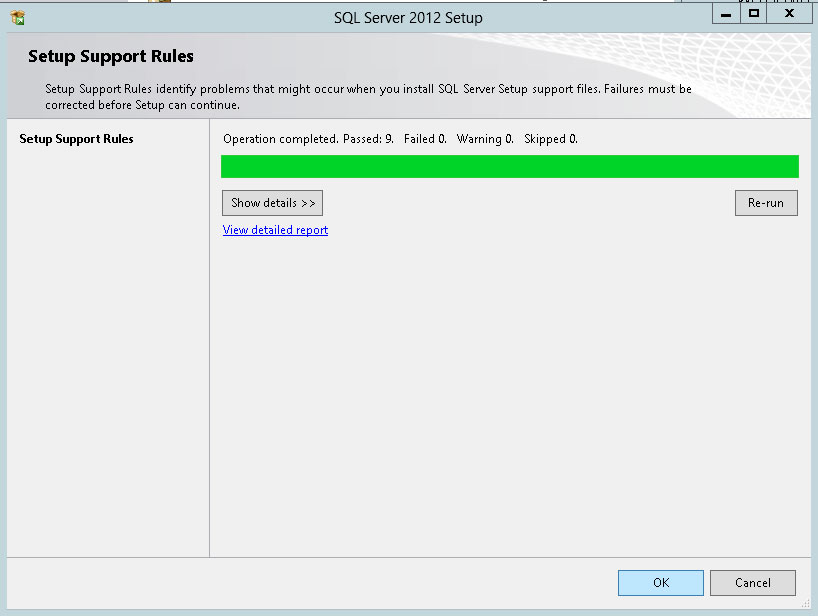


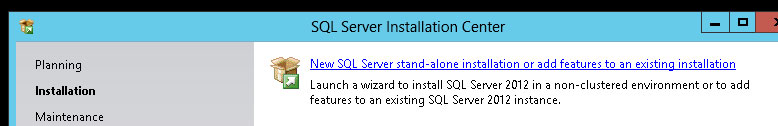
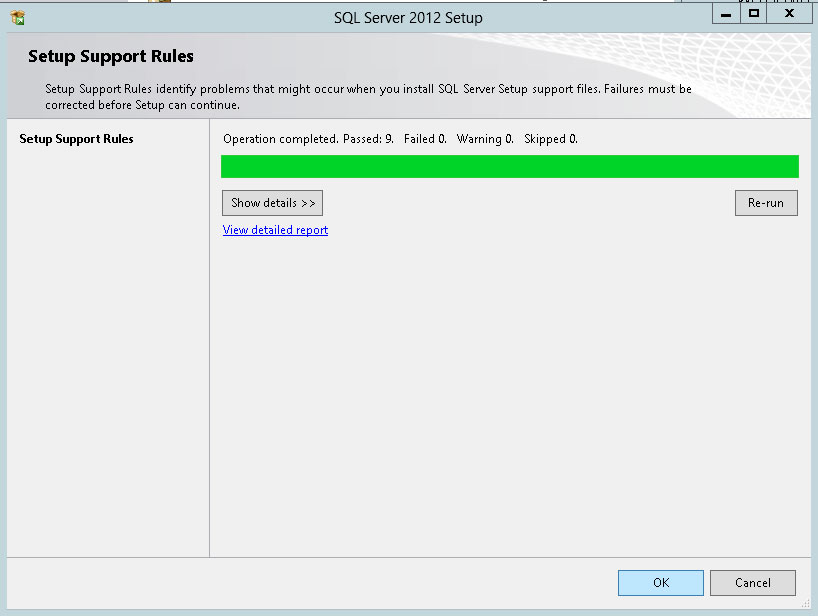
However, when I got the step that would allow me to install the feature, it indicated it had already been installed.

Thus I thought the solution was to re-install it, but this was as far as the SQL 2012 SP1 disc would take me in terms of reinstalling. To get around this, I first attempted to uninstall the feature through Control Panel / Programs. However, that gave me an error message : ‘Install-SPRSServiceInstall-SPRSService’ is not recognized, when I got to the final uninstall step.
I unprovisioned the service application in Central Admin, and STOPPED the service on the server, and tried again. No luck.
Also , attempting to uninstall the application through Powershell yielded the same “not recognized” results using the following uninstall commands:
Install-SPRSService -uninstall
Install-SPRSServiceProxy -uninstall
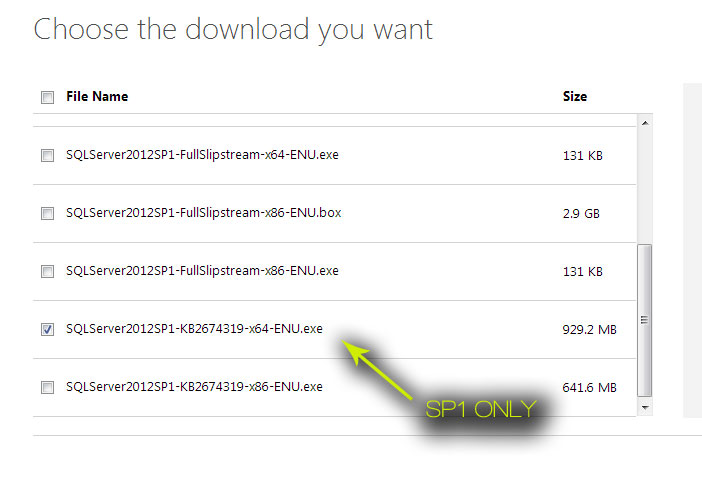
Finally, I discovered a solution. It turns out that the full installation disc for SQL 2012 SP1 apparently was not sufficient. Instead, just the SP1 exe need to be installed on top of what is already there, not the full install of SQL 2012 SP1, but just the SP1 bits.
Download it here: http://www.microsoft.com/en-us/download/details.aspx?id=35575
Be sure to choose the correct download, and not the full version.
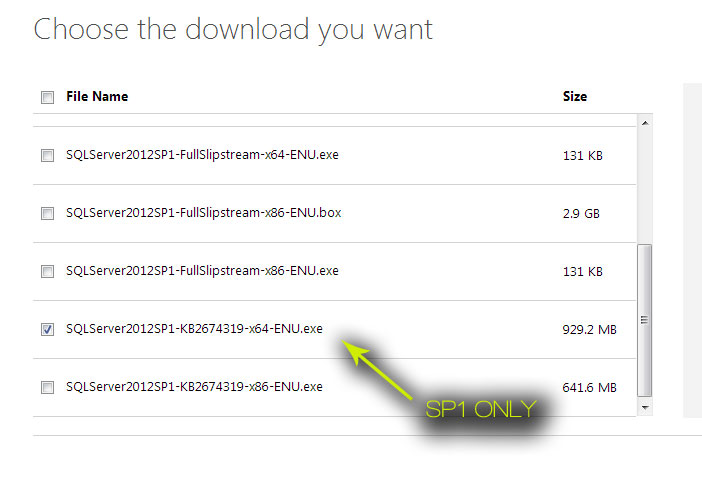
After grabbing this, run the install.

Verify that that “Reporting” folder is now present.
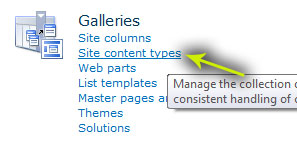
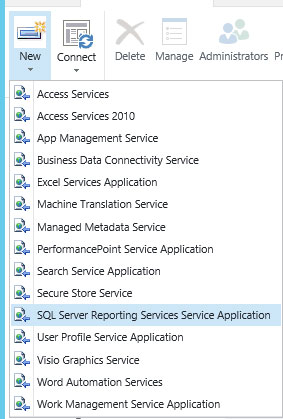
Finally, you can provision your services:
Install-SPRSService
Install-SPRSServiceProxy
get-spserviceinstance -all |where {$_.TypeName -like "SQL Server Reporting*"} | Start-SPServiceInstance
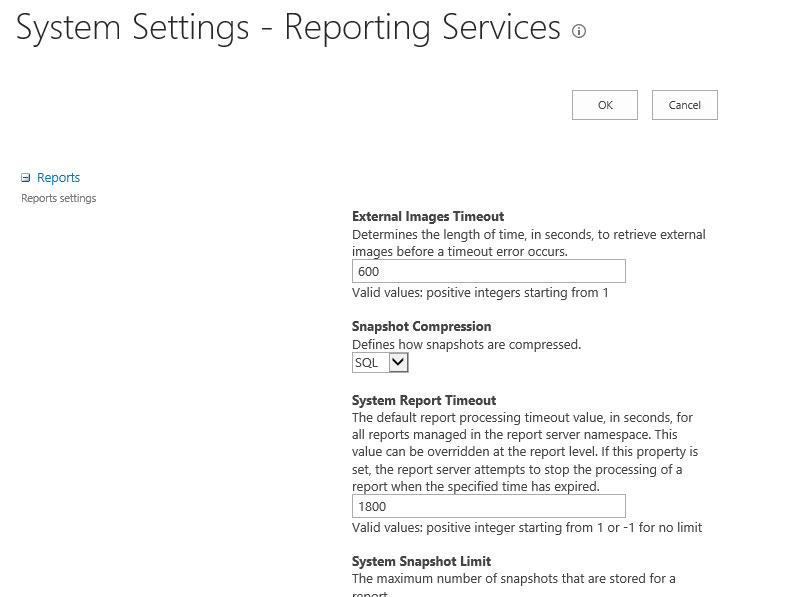
Then click on “System Settings” in your app.
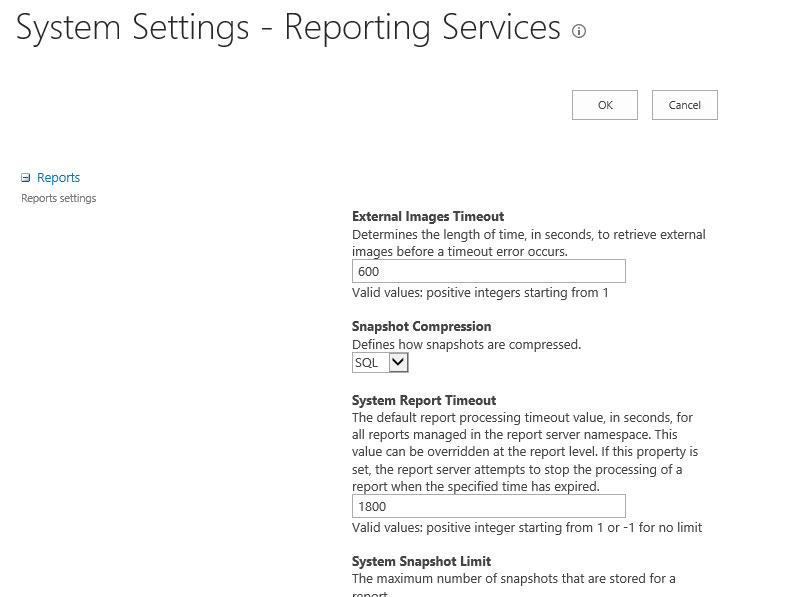
Success!!!
![]()